Cybersecurity Incident Response
Services
Cybersecurity Incident Response
Services
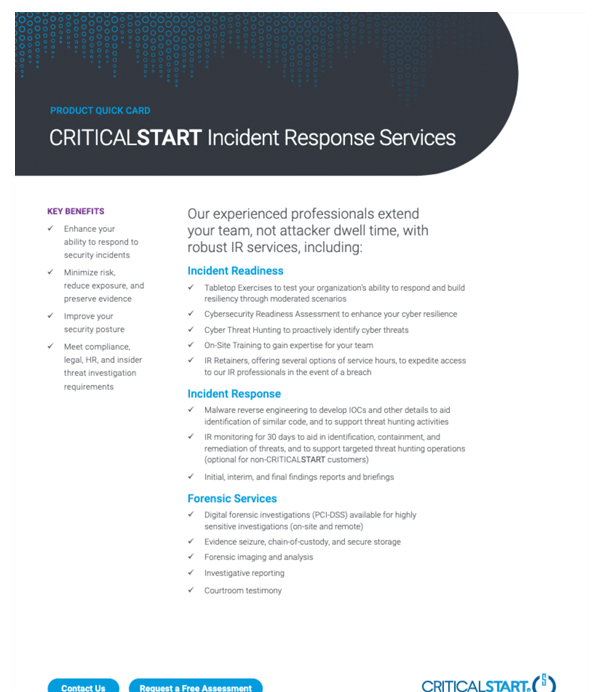
Breaches happen in today’s complex, technological world, but you have the power to do something about it. Our Cybersecurity Incident Response team helps you limit the dwell time of an attacker through immediate response.
We also proactively work with you to understand your preparedness with Incident Response (IR) readiness services including full security incident and compromise scoping, triage, investigation, containment, eradication, remediation and recovery to help you build a robust incident response plan. Our Incident Response retainers offer several options service hours, and any unused hours may be applied to other services engagements.

Proactive Planning & Strategy—a customer-focused approach to ensure organizational readiness
IR retainers—several options for as-needed service hours; any unused hours may be applied to other services, such as penetration testing
Digital forensics investigations (PCI-DSS) available for highly sensitive investigations
Our simple and cost-effective packages include one flat price for total team hours, regardless of how many different team members work on the project. Any unused hours can be applied to other Cybersecurity IR engagements.
Our Incident Response retainers offer the flexibility to access experts for emergency response or for incident readiness services to help you prepare for an imminent event.
Minimize risk, reduce exposure, and preserve evidence as our team coordinates and responds quickly—critical to stopping a breach.
A Cyber Incident Response Engagements include thirty days of endpoint monitoring for increased security.
Test your organization’s ability to respond and build resiliency through moderated scenarios including simulated cyberattacks, disaster recovery and other crises.
Enhance your cyber resilience through an assessment of all aspects of your cyber defense operations, including an evaluation of opportunities for improving security architecture, tools and processes.
Proactively identify cyber threats through hypothesis-driven analysis across your network or specified hosts based on investigative leads or Indicators of Compromise (IoCs).
Gain expertise for your team through experienced instructor-led training in memory analysis, host forensics, network forensics, threat monitoring and investigation/incident response.
Meet compliance, legal, HR and insider threat investigation requirements through our forensic services for sensitive investigations.
Use dynamic and static analysis of suspicious and/or malicious code to develop IOCs and other details to aid identification of similar code, and to support threat hunting activities.
Receive regularly scheduled client briefings as well as interim and final investigative findings reports and lessons learned.
Deploy our EDR agents across your network or subset of endpoints to aid in the identification, containment and remediation of threats, and to support targeted threat hunting operations.

Breaches are a fact of life for every business. However, it is possible to stop breaches and improve your security posture by taking a proactive approach to your Cyber Incident Response (IR) strategy.
When your organization is under cyberattack, an immediate response is critical. The longer the dwell time, the more damage is done.

When the COVID-19 pandemic began, this company kept its distribution center in operation but shifted 85-90% of its office staff to remote work to ensure product continued to reach customers and exceed their expectations. This move to remote work brought with it a new set of challenges.
Combine an IR retainer with Managed Detection and Response (MDR) services.
CRITICALSTART Managed Detection and Response services provide 24x7x365 SOC expertise and integrations with industry leading EDR, SIEM, and XDR technologies to quickly detect every event, resolve every alert and respond to breaches. MDR excels in protecting customer data, stopping ransomware in its tracks, and optimizing your existing security investments.