Incident Response Monitoring
EXPLORE SERVICES
Our IR Monitoring service leverages the power of our Zero-Trust Analytics Platform® (ZTAP®) to bring surgical precision to every IR engagement.
This service, which is optional for non-Critical Start customers, includes:
Active 24×7 monitoring of all alerts by seasoned professionals and purpose-built technology

SOC augmentation for 24×7 event detection and triage

Alert escalation based on your threat assessment and impact analysis
Ability to leverage industry-vertical playbooks and threat intelligence
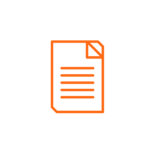
30-day demo license for integrated EDR products

Key Benefits
Identify, contain and remediate threats
Block malware processes and contain breaches
Support threat hunting operations during a breach
Contain Breaches Across Diverse Attack Vectors
We handle criminal and non-criminal matters related to a wide variety of incidents, including:
- Malware-based attacks (Ransomware, Trojans, etc.)
- Phishing attacks
- Zero-Day attacks
- Password attacks
- IoT attacks
- Critical infrastructure attacks
- Cryptojacking
- Insider threats (espionage, fraud, etc.)
- Financial crimes
- Business email compromise