Our new Partner Portal is now live on Salesforce Communities, with new features and capabilities as you ready your business for the new year. Best wishes as you refresh and enjoy the holiday season. Now here’s your quick roundup of news, events, and updates to help your business thrive.

Partner Portal Announcement
CRITICALSTART’s NEW Partner Portal through Salesforce Communities is now live! This move to Salesforce Communities will allow our partner community more visibility and hands-on access to deal registrations, leads, marketing content, and more.
If you had a previous partner portal login, you received an email on November 14 with login instructions from Salesforce PRM Communities. Please follow the directions in the email to login to the portal.
If you are new to the Partner Portal, please apply here.
SPIFF Update
Our Managed Detection and Response SPIFF program promotion runs through January 31, 2022. Don’t miss your chance to claim these payouts:
SALES DEMO SPIFF – $500 each to Sales Rep and SE for a registered opportunity and demo meeting scheduled and held.
CLOSED DEAL SPIFF – Starting at $1,000 and up to $7,000.
Eligible Vendors + CRITICALSTART MDR
(Microsoft Azure Sentinel, Microsoft Defender Endpoint, Palo Alto Networks, Carbon Black Response, CrowdStrike, CylancePROTECT, Devo, SentinelOne, Splunk)
For additional details, please contact your Channel Manager.


Win of the Month
A publicly traded facility management company with annual revenues of $6B and more than 100,000 employees wanted to free up their security team to focus on additional security tasks and reduce the enterprise’s overall risk level.
The right solution would need the ability to see and react to alerts coming from Microsoft Defender for Endpoint and Microsoft Azure Sentinel, so the company could achieve full ROI on their security tool investments.
The customer chose CRITICALSTART Managed Detection and Response services in a one-year deal, worth $495K to the channel partner. During the 60-day sales cycle, our MDR service delivery model aligned with the customer’s defined success criteria to beat out BlueVoyant and replaced Dell SecureWorks threat intelligence.
Key requirements included expertise in the Microsoft security stack, a US-based SOC, contractual SLAs, expert-level response capabilities, and the ability for the customer to access provider-collected data in a transparent manner.
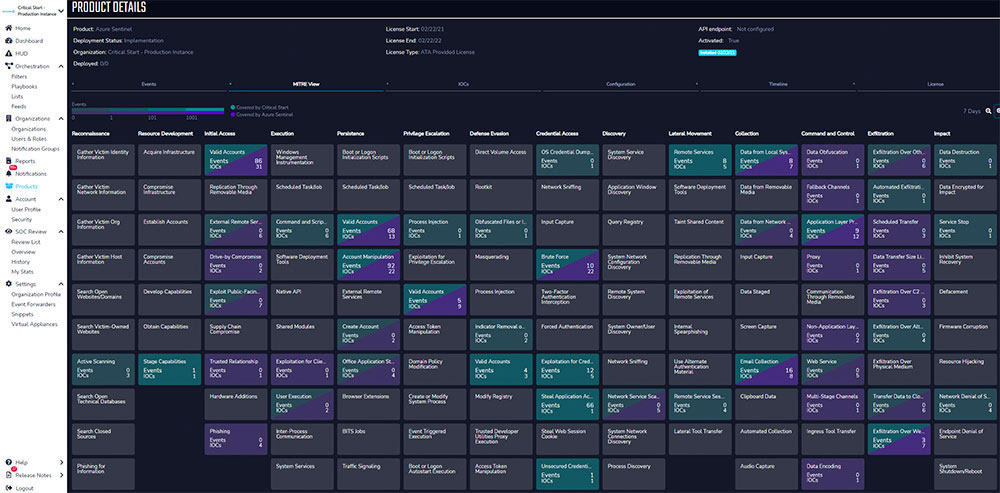
CRITICALSTART Threat Navigator
CRITICALSTART Managed Detection and Response (MDR) services for Microsoft, Splunk, Devo, and SentinelOne* now include a new no-cost feature: CRITICALSTART Threat Navigator.
Threat Navigator helps our Cyber Research Unit manage the hundreds of detection rules generated by the security tool, the custom content we produce based on curated threat intel, and the constant rewriting of detection rules.
This feature delivers more robust context to our SOC analysts so they can make quicker, more precise decisions when investigating potential threats in a customer’s environment and consistently communicate about the customer’s security posture.
Key customer benefits include:
- Enriches alerts as they are ingested into ZTAP with open-source detections, out-of-the-box SIEM/EPP/EDR vendor detections, and threat detection content we produce, making it faster and easier for our SOC analysts and customers to respond.
- Provides customers full transparency into the threat detections provided out-of-the-box, detections developed by CRITICALSTART, and the actual queries and rules we develop for our customers.
- Notifies customers when a new Indicator of Compromise is added to ZTAP and how it maps to the MITRE ATT&CK® framework to help detect more attacks.
For more customer benefits and details, see the Cyber Research Unit – Threat Navigator folder in the or contact your CRITICALSTART SC. Stay tuned for details on a January 2022 training session we will offer on these offerings.
*Support for Threat Navigator for CrowdStrike, VMWare CarbonBlack, and Palo Alto is slated for GA in January 2022.

Palo Alto Networks Cortex™ XSOAR and ServiceNow
Cortex XSOAR is a comprehensive security orchestration, automation, and response (SOAR) platform that unifies case management, automation, real-time collaboration, and threat intel management to serve security teams across the incident lifecycle.
For customers of CRITICALSTART and Palo Alto Networks who use XSOAR as their “single pane of glass” orchestration tool, this bi-directional sync between XSOAR and our Zero Trust Analytics Platform (ZTAP) will deliver immediate value to them. That’s because it fits into their existing workflows without requiring the customer analyst to pivot to ZTAP unless desired.
The ZTAP app is available for download within the XSOAR Marketplace in the customer’s Cortex XSOAR console.
ServiceNow is a workflow automation platform and ticketing tool that enables organizations to improve operational efficiencies. ServiceNow streamlines and automates routine work tasks to resolve everyday internal IT issues that process and catalog customer service requests.
For customers of ServiceNow and CRITICALSTART, this bi-directional sync between ServiceNow and ZTAP allows them to monitor alerts and share information more effectively. They can address critical incidents in real time without leaving the ServiceNow interface.
The ZTAP app is available for download via the ServiceNow Store.
For additional information about these integrations, please contact your Channel Account Manager.
In The News
In this blog post, we detail a range of threats facing the shipping industry, offer actionable solutions, and provide a downloadable summary of our November Cyber Threat Intelligence Report.
Connected technologies that make cities smarter can also make cities more vulnerable. Read our latest blog on solutions like encryption, identity governance, and other super smart ideas that address these vulnerabilities.
There’s a new malware endgame – but we know how to address it, and more importantly, how to prevent it. In our latest blog post, we soothe fears around sinister-sounding killware and offer some cybersecurity remedies to keep healthcare and other critical infrastructures safe.
Events
Join our webinars!
- In Cybersecurity Every Alert Matters – January 12, 2022 at Noon CT. CRITICALSTART CTO Randy Watkins and IDC Program Director – Security Services Craig Robinson discuss results from the CRITICALSTART-sponsored IDC white paper. Register here.
- Healthcare vertical webinar on January 26th, register here.
See us in person at RSA Conference 2022 – February 7-10 in San Francisco! The Critical Start booth will be in the South Hall at Booth #1861. You can also join us for a Partner Appreciation Lunch on Tuesday, Feb. 8 from 11-1pm PST. Register here.