Incident Response Services
EXPLORE SERVICES
How we do it
Crisis Management
Leverage our Cyber Incident Response Team (CIRT) to lead your team through critical stages of an incident.
We handle criminal and non-criminal matters related to a wide variety of incidents, including:
- Malware-based attacks (Ransomware, Trojans, etc.)
- Phishing attacks
- Zero-Day attacks
- Password attacks
- IoT attacks
- Critical infrastructure attacks
- Cryptojacking
- Insider threats (espionage, fraud, etc.)
- Financial crimes
- Business email compromise
Threat Hunting
Our MDR platform and U.S.-based SOC provide 24x7x365 detection/investigation/continuous threat hunting and response. Alternatively, you can use our Threat Hunting Training services to prepare your own defenders to proactively identify malicious activity within your network and take appropriate action.
Reports & Debrief
Receive regularly scheduled briefings as well as interim and final investigative findings reports and lessons learned.
Malware Reverse Engineering
Our CIRT uses dynamic and static analysis of suspicious and/or malicious code to develop IOCs and other details to aid identification of similar code, and to support threat hunting activities.
Quick Card
Cyber Incident Response Team (CIRT) Services
This solution quick card discusses the robust incident readiness, incident response and forensic services provided by our CIRT.
DATA SHEET
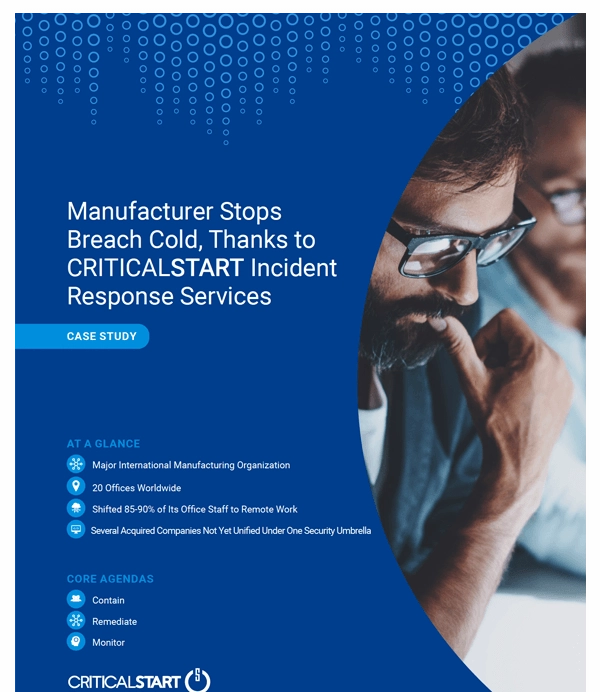
Manufacturer Stops Breach Cold, Thanks to Critical Start Incident Response Services
When the COVID-19 pandemic began, this company kept its distribution center in operation but shifted 85-90% of its office staff to remote work to ensure product continued to reach customers and exceed their expectations. This move to remote work brought with it a new set of challenges.