Chris Ward speaks with Quentin Rhoads-Herrera of CRITICALSTART to discuss cybersecurity in a time of a pandemic.
In our current time of crisis, it’s a sad fact that there are many taking advantage of distracted governments, businesses, and individuals. With the majority of workforces in the Western world currently working from home, often on insecure networks, and far removed from their typical IT support structure, an increase in cybersecurity threats has reared its head during the COVID-19 crisis.
I recently spoke with Quentin Rhoads-Herrera of CRITICALSTART to discuss trends they have recently witnessed, how the company is helping during the crisis, and cutting through some cybersecurity jargon. You can hear the full interview above.
Disinformation
I spoke with Quentin several weeks ago, and in the weeks since, the disinformation has increased, especially as the crisis took its hold in Europe and the US. During our interview. He mentioned that his team had noticed a rapid ramping up of domain purchases relating to COVID-19 and Coronavirus, and increased Twitter (frequently bot or spoof accounts) activity, spreading incorrect information as fast as the virus itself.
This is not the first time Quentin and his team have had to respond to increased activity, and major events typically trigger a flurry of activity in those corners of the web that many of us live in blissful ignorance of.
For example, when the US announced Space Force there was a rush to register similar domains to cause confusion. Whenever there is a mass of information on a particular topic, there will be an equal amount of disinformation. The announcements of various stimulus packages around the world added to the disinformation campaign, if there is a lot of money involved, you can guarantee that others will attempt to trick people into parting with it, even in a time of crisis.
Though Quentin took pains to point at that with the COVID-19 pandemic, the modern world has never seen a crisis of such a global scale. Equally, the cybersecurity community has never seen a reaction to that at such a scale either.
Phishing Attacks
Many of these fake domains are also used for targeted or mass attacks using Phishing techniques. Many of these phishing attempts promise cures, masks, or “official” information from government bodies, such as the CDC. While the human factor has always been the easiest route for any hack, the added factors of stress, distraction (from working around family members, etc.), and insecure work environments, as I mentioned above, have made it an easier play. Google also recently announced how many (18 million)c false emails they are blocking EVERY day.
Practice Safe Security
Cybersecurity doesn’t change so much in a time of crisis, just that the potential attack vectors change. As with any other time, you should treat any email that isn’t from someone you know (or looks different than it typically does) as potentially malicious. You should make sure you’ve changed the default admin account details on your router, use a VPN, or PGP signing, multi-factor authentication, etc. But we all know that these are not always the easiest tasks for everyone to understand and implement, and even then, malicious parties can lead them astray and cause even more harm.
Lend a Technical Hand
Now, at least a few weeks into the crisis for most countries, I’m sure IT support staff have had many a VoIP call with staff members attempting to help them get set up as securely and simply as possible. This task is made even more difficult by pressures on home internet performance, and other external pressures. I’m sure many of you reading this have helped out relatives, colleagues and friends with IT issues over the past few weeks, and this continues to be a great way tech-minded folks like us can help those around us who are struggling to cope with a lot of unknowns right now.
Another place we can help is by using our know-how and computing power to contribute to projects, such as folding@home (for protein model simulations) or a multitude of hackathons (some specific open source ones too) in local and global areas.
CRITICALSTART has dedicated a proportion of their hash cracking machines that are normally used to test password encryption security to the folding@home project, and even Blockchain miners are starting to switch some of their machines to help.
At the moment, one of the best skills (as developers and other tech-minded folks) we can learn to help others through this crisis is a large dose of patience and understanding.
A Cybersecurity Primer
While we’re on the topic, here are some key terms and concepts.
Team Structure
Cybersecurity companies tend to divide themselves into different teams, loosely around offensive actions (sometimes called a penetration tester) called a red team to find vulnerabilities, and defensive team, called a blue team, to help fix those vulnerabilities.
Managed Detection and Response (MDR)
A newer approach to security practices, where a team helps a client manage their security infrastructure by collecting logs from endpoints such as antivirus and threat detection systems, matching them to a registry of known “good” and “bad” alerts and actions to detect real issues.
This analysis can become quite nuanced, for example, allowing some users to run scripts, such as Powershell or bash scripts, but raising an alert if another user trues the same.
Zero-day
A zero-day is a vulnerability that the world does not know about yet. A vendor may know about it because someone told them about it, a client may know about it because it was found during a client engagement, but nobody else in the world knows about it. Generally, a team helps a vendor patch the issue and ensure that their clients have applied the patch. If the vendor never responds, then a team helps the client work around the patch as much as possible.
Featured in DZone | April 22, 2020
![]()
Ransomware in 2025: The Real Risk, the Gaps That Persist, and What Actually Works
Ransomware attacks aren’t slowing down. They’re getting smarter, faster, and more expensive. In ...![]()
Security Operations Leaders: The Chaos Is Real
If you’re a CISO, SOC leader, or InfoSec pro, you’ve felt it. Alert volumes spike. Tools multipl...![]()
Transform Vulnerability Management: How Critical Start & Qualys Reduce Cyber Risk
In a recent webinar co-hosted by Qualys and Critical Start, experts from both organizations discusse...![]()
H2 2024 Cyber Threat Intelligence Report: Key Takeaways for Security Leaders
In a recent Critical Start webinar, cyber threat intelligence experts shared key findings from the H...![]()
Bridging the Cybersecurity Skills Gap with Critical Start’s MDR Expertise
During a recent webinar hosted by CyberEdge, Steven Rosenthal, Director of Product Management at Cri...![]()
2024: The Cybersecurity Year in Review
A CISO’s Perspective on the Evolving Threat Landscape and Strategic Response Introduction 2024 has...![]()
Modern MDR That Adapts to Your Needs: Tailored, Flexible Security for Today’s Threats
Every organization faces unique challenges in today’s dynamic threat landscape. Whether you’re m...![]()
Achieving Cyber Resilience with Integrated Threat Exposure Management
Welcome to the third and final installment of our three-part series Driving Cyber Resilience with Hu...Why Remote Containment and Active Response Are Non-Negotiables in MDR
You Don’t Have to Settle for MDR That Sucks Welcome to the second installment of our three-part bl...![]()
Choosing the Right MDR Solution: The Key to Peace of Mind and Operational Continuity
Imagine this: an attacker breaches your network, and while traditional defenses scramble to catch up...![]()
Redefining Cybersecurity Operations: How New Cyber Operations Risk & Response™ (CORR) platform Features Deliver Unmatched Efficiency and Risk Mitigation
The latest Cyber Operations Risk & Response™ (CORR) platform release introduces groundbreaking...![]()
The Rising Importance of Human Expertise in Cybersecurity
Welcome to Part 1 of our three-part series, Driving Cyber Resilience with Human-Driven MDR: Insights...![]()
Achieving True Protection with Complete Signal Coverage
Cybersecurity professionals know all too well that visibility into potential threats is no longer a ...![]()
Beyond Traditional MDR: Why Modern Organizations Need Advanced Threat Detection
You Don’t Have to Settle for MDR That Sucks Frustrated with the conventional security measures pro...The Power of Human-Driven Cybersecurity: Why Automation Alone Isn’t Enough
Cyber threats are increasingly sophisticated, and bad actors are attacking organizations with greate...Importance of SOC Signal Assurance in MDR Solutions
In the dynamic and increasingly complex field of cybersecurity, ensuring the efficiency and effectiv...The Hidden Risks: Unmonitored Assets and Their Impact on MDR Effectiveness
In the realm of cybersecurity, the effectiveness of Managed Detection and Response (MDR) services hi...![]()
The Need for Symbiotic Cybersecurity Strategies | Part 2: Integrating Proactive Security Intelligence into MDR
In Part 1 of this series, The Need for Symbiotic Cybersecurity Strategies, we explored the critical ...Finding the Right Candidate for Digital Forensics and Incident Response: What to Ask and Why During an Interview
So, you’re looking to add a digital forensics and incident response (DFIR) expert to your team. Gr...![]()
The Need for Symbiotic Cybersecurity Strategies | Part I
Since the 1980s, Detect and Respond cybersecurity solutions have evolved in response to emerging cyb...![]()
Critical Start H1 2024 Cyber Threat Intelligence Report
Critical Start is thrilled to announce the release of the Critical Start H1 2024 Cyber Threat Intell...![]()
Now Available! Critical Start Vulnerability Prioritization – Your Answer to Preemptive Cyber Defense.
Organizations understand that effective vulnerability management is critical to reducing their cyber...![]()
Recruiter phishing leads to more_eggs infection
With additional investigative and analytical contributions by Kevin Olson, Principal Security Analys...![]()
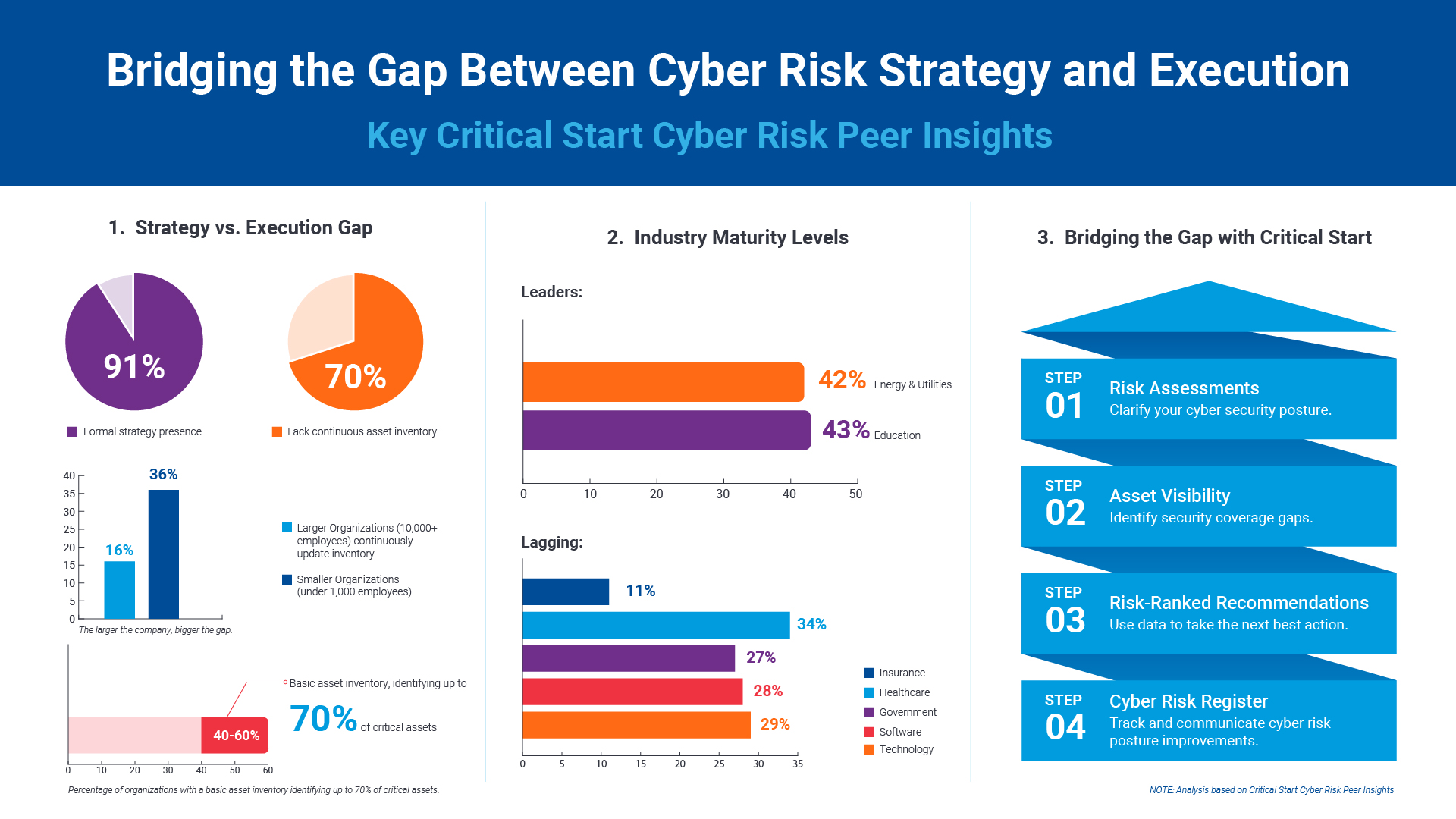
2024 Critical Start Cyber Risk Landscape Peer Report Now Available
We are excited to announce the release of the 2024 Critical Start Cyber Risk Landscape Peer Report, ...Critical Start Managed XDR Webinar — Increase Threat Protection, Reduce Risk, and Optimize Operational Costs
Did you miss our recent webinar, Stop Drowning in Logs: How Tailored Log Management and Premier Thre...Pulling the Unified Audit Log
During a Business Email Compromise (BEC) investigation, one of the most valuable logs is the Unified...![]()
Set Your Organization Up for Risk Reduction with the Critical Start Vulnerability Management Service
With cyber threats and vulnerabilities constantly evolving, it’s essential that organizations take...![]()
Announcing the Latest Cyber Threat Intelligence Report: Unveiling the New FakeBat Variant
Critical Start announces the release of its latest Cyber Threat Intelligence Report, focusing on a f...Cyber Risk Registers, Risk Dashboards, and Risk Lifecycle Management for Improved Risk Reduction
Just one of the daunting tasks Chief Information Security Officers (CISOs) face is identifying, trac...![]()
Beyond SIEM: Elevate Your Threat Protection with a Seamless User Experience
Unraveling Cybersecurity Challenges In our recent webinar, Beyond SIEM: Elevating Threat Prote...![]()
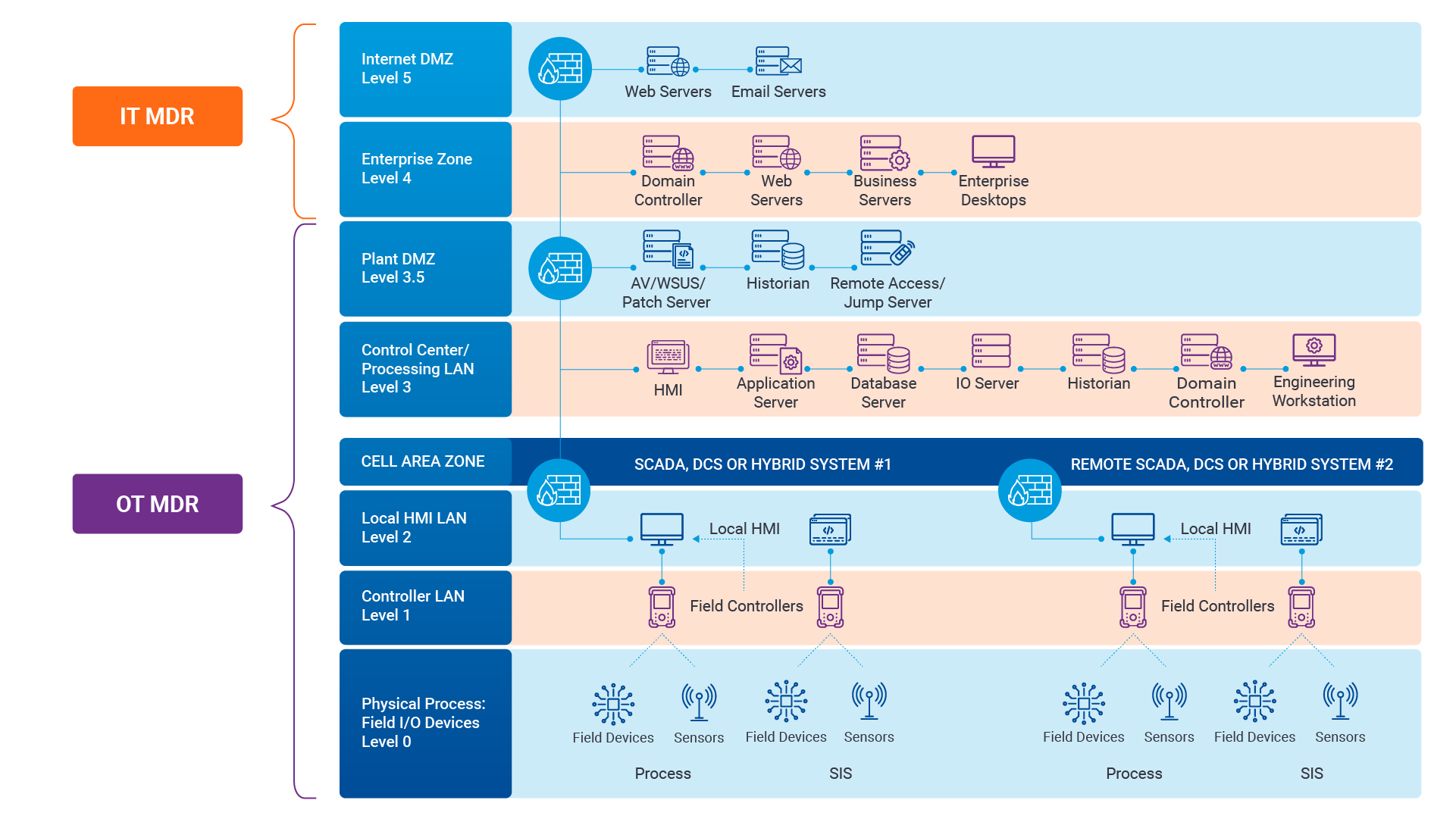
Navigating the Convergence of IT and OT Security to Monitor and Prevent Cyberattacks in Industrial Environments
The blog Mitigating Industry 4.0 Cyber Risks discussed how the continual digitization of the manufac...![]()
Critical Start Cyber Risk Peer Insights – Strategy vs. Execution
Effective cyber risk management is more crucial than ever for organizations across all industries. C...![]() Press Release
Press ReleaseCritical Start Named a Major Player in IDC MarketScape for Emerging Managed Detection and Response Services 2024
Critical Start is proud to be recognized as a Major Player in the IDC MarketScape: Worldwide Emergin...Introducing Free Quick Start Cyber Risk Assessments with Peer Benchmark Data
We asked industry leaders to name some of their biggest struggles around cyber risk, and they answer...Efficient Incident Response: Extracting and Analyzing Veeam .vbk Files for Forensic Analysis
Introduction Incident response requires a forensic analysis of available evidence from hosts and oth...![]()
Mitigating Industry 4.0 Cyber Risks
As the manufacturing industry progresses through the stages of the Fourth Industrial Revolution, fro...![]()
CISO Perspective with George Jones: Building a Resilient Vulnerability Management Program
In the evolving landscape of cybersecurity, the significance of vulnerability management cannot be o...![]()
Navigating the Cyber World: Understanding Risks, Vulnerabilities, and Threats
Cyber risks, cyber threats, and cyber vulnerabilities are closely related concepts, but each plays a...The Next Evolution in Cybersecurity — Combining Proactive and Reactive Controls for Superior Risk Management
Evolve Your Cybersecurity Program to a balanced approach that prioritizes both Reactive and Proactiv...![]()
CISO Perspective with George Jones: The Top 10 Metrics for Evaluating Asset Visibility Programs
Organizations face a multitude of threats ranging from sophisticated cyberattacks to regulatory comp...- Webinar
Are Critical Threats Slipping Through Your Defenses?
Modern security teams are buried in noisy alerts and stretched thin. Even with powerful tools like M... ![]()
Ransomware in Gaming: How Casinos Can Defend Against Modern Cyber Threats
Hackers aren’t gambling. They know exactly where to hit. And for gaming companies, the stakes ...- eBook
Ditch the Black Box: Get Transparent MDR with Critical Start
Tired of MDR providers leaving you in the dark? We totally get it. Our eBook, Unmatched Transparency...
Newsletter Signup
Stay up-to-date on the latest resources and news from CRITICALSTART.
Thanks for signing up!