Jordan Mauriello, SVP of Managed Security, shares his thoughts with Steve Gruber of the Steve Gruber Podcast on election security and the vulnerabilities associated with polling places in light of the coming 2020 elections.
Full Video Transcript:
SG: It is six states going to the polls today, and critical states. Bernie Sanders would like nothing more than to repeat his upset victory that he claimed in Michigan four years ago when he beat Hillary Clinton, who was supposedly up by 20 points – 27 points one poll had her up before the primary in Michigan. And Bernie Sanders came in and pulled it off.
What about the vulnerability of polling places when it comes to online impacts, cyber impacts, cyberattacks? Jordan Mauriello here, CRITICALSTART‘s VP of Managed Security. Jordan, welcome to the program.
JM: Thank you very much, Steve. Happy to be with you this morning.
SG: So my understanding Jordan, is that most of these election machines, the tabulation machines, the computers themselves are not connected directly to the internet. But then I talk and hear from people who say, “Now wait a second, we’re gonna make it possible to vote online.” Well, obviously, if you’re voting online, you’re connected to the internet directly. What should be my concerns? Where are the vulnerabilities?
JM: So there’s definitely a lot of confusion about what the technology actually does in voting machines these days and the reason for that is it is, actually, different state to state in a lot of places. We see places like Iowa, which set a precedent for, oh, there’s an app, and online technology for voting that is being used, and clearly had significant technological issues, not to mention the lack of proper security assessment that was actually done there. So there were vulnerabilities that were introduced and significant problems as a part of the election.
But mostly what we’re actually seeing is a move towards an upgraded ballot marking device, or a device which eventually transfers votes through some, kind of, centralized system that is online, but then uploads those votes for a digital count mechanism. That’s where a lot of times we see the vulnerability mechanisms are actually introduced, is when we centralize this. But there’s always some way that they’re being connected to a network and being tabulated.
SG: So, the vulnerabilities, in your line of work, then, you go through and you say, “Okay, I see a weakness here, I see a weakness here.” Is that how you approach your job?
JM: Yeah. And that’s, often, what organizations bring us in to do, is to attempt to find what are the mechanisms to which something might be compromised. And, so, when we’re looking at election security specifically, you know, if we’re looking at in ballot marking devices, a good example of this is, the new devices they purchased in South Carolina, right? It’s like, “Oh, great it’s a ballot marking device.” And so you’re gonna use a screen, a touch screen to make your selection, and it’s gonna print out a ballot, it’s marked it for you. But then when it reads back in, what it actually reads is the bar code at the bottom.
And so, if you were a malicious activist, especially with someone with the kind of resources that a foreign nation-state would have that want to disrupt elections, well, you could certainly compromise that machine. As it prints out the proper results, when you’re validating, look it printed, “Oh, yes, I voted for Joe Biden. Yes, I voted for Bernie Sanders.” But then the bar code, well none of these humans that can read a bar code right now. So, you would feed that back in and not know what the bar code might actually register back to the device itself and that is a vulnerability.
SG: Yeah. Jordan, I know enough people that have enough difficulty reading period. Barcodes, I mean, let’s talk about that’s a little bit tougher.
Jordan Mauriello here, CRITICALSTART‘s VP of Managed Security.
So, let me ask you this. When you go in and vote yourself, I assume you vote-
JM: Yes sir.
SG: Do you have concerns about the security of your vote? Do you, do you have much security concerns overall when it comes to the reliability and accuracy of elections across this country?
JM: I think we saw, based on the 2016 elections, and what happened both at the campaign level and with evidence that’s come out from Durham County, North Carolina, that there definitely are problems and there are concerns that I have.
As a security expert, I look at the process they plan on. I’m definitely gonna go in, I’m gonna double-check my vote. I’m gonna look at the printout and make it sure it matches as best I can. I’m gonna feed it back in the device and make sure it says what I actually did, as being registered on the screen again. But I also had concerns at the campaign level.
And we saw the detriment that the cybersecurity problems were, like Hillary Clinton’s campaign in 2016. And those are very, very real issues. When you’re talking about the resources and capability that a foreign nation-state has in cyber warfare and applying that against not just election infrastructure, but even campaigns. There’s definitely significant concerns that both at an information and disinformation level, and an election security equipment level, that things could be compromised or disrupted.
SG: Well, and that’s a big concern obviously. I’m more concerned, honestly, in the way they’re tryin’ to do it in an old-fashioned way. What I mean by that is, you look at mail-in ballots. I think they’re more susceptible to fraud, potentially, the way it’s set up. Certainly in California with ballot harvesting and so forth. But, as you look forward then, Jordan, do you see a better situation? Are you more confident, more optimistic as you look at the future with more technology, more safety standards and protocols put in place? What do you make of it?
JM: So, I think we’ve made some very strong decisions in the last four years now to help improve election security, but it’s a slow process. It’s not happening overnight. We created the cybersecurity infrastructure and security agency in 2018, but there’s still a lot of things that have to be accomplished as a part of that.
And I think, Homeland Security, the committee and subcommittee on cybersecurity and privacy are moving in the right direction, being led by a lot of the right people, but there are a lot of things that we have to train election officials on. Have to educate, have to put the right equipment in place.
There are problems with even hard ballots and mail-in ballots that need to be approached from a process perspective, but then the technological issues and even the desire for some states to move to electronic voting introduces a whole new level of vulnerability that genuinely we are not prepared for from an election infrastructure perspective yet, and that has to be approached with the right mindset.
And I know a lot of people have asked, “Hey, are we moving to online voting?” and the real answer is, I hope not, because we are not ready, in the election infrastructure to actually do that yet.
SG: And I think we should leave it right there. We are not ready for that, and yet they keep pushing ideas ahead. Jordan Mauriello, CRITICALSTART‘s VP of Managed Security.
Jordan, greatly appreciate your insight in the conversation today.
JM: Thank you, Steve. It was a pleasure to be with you, sir.
![]()
Ransomware in 2025: The Real Risk, the Gaps That Persist, and What Actually Works
Ransomware attacks aren’t slowing down. They’re getting smarter, faster, and more expensive. In ...![]()
Security Operations Leaders: The Chaos Is Real
If you’re a CISO, SOC leader, or InfoSec pro, you’ve felt it. Alert volumes spike. Tools multipl...![]()
Transform Vulnerability Management: How Critical Start & Qualys Reduce Cyber Risk
In a recent webinar co-hosted by Qualys and Critical Start, experts from both organizations discusse...![]()
H2 2024 Cyber Threat Intelligence Report: Key Takeaways for Security Leaders
In a recent Critical Start webinar, cyber threat intelligence experts shared key findings from the H...![]()
Bridging the Cybersecurity Skills Gap with Critical Start’s MDR Expertise
During a recent webinar hosted by CyberEdge, Steven Rosenthal, Director of Product Management at Cri...![]()
2024: The Cybersecurity Year in Review
A CISO’s Perspective on the Evolving Threat Landscape and Strategic Response Introduction 2024 has...![]()
Modern MDR That Adapts to Your Needs: Tailored, Flexible Security for Today’s Threats
Every organization faces unique challenges in today’s dynamic threat landscape. Whether you’re m...![]()
Achieving Cyber Resilience with Integrated Threat Exposure Management
Welcome to the third and final installment of our three-part series Driving Cyber Resilience with Hu...Why Remote Containment and Active Response Are Non-Negotiables in MDR
You Don’t Have to Settle for MDR That Sucks Welcome to the second installment of our three-part bl...![]()
Choosing the Right MDR Solution: The Key to Peace of Mind and Operational Continuity
Imagine this: an attacker breaches your network, and while traditional defenses scramble to catch up...![]()
Redefining Cybersecurity Operations: How New Cyber Operations Risk & Response™ (CORR) platform Features Deliver Unmatched Efficiency and Risk Mitigation
The latest Cyber Operations Risk & Response™ (CORR) platform release introduces groundbreaking...![]()
The Rising Importance of Human Expertise in Cybersecurity
Welcome to Part 1 of our three-part series, Driving Cyber Resilience with Human-Driven MDR: Insights...![]()
Achieving True Protection with Complete Signal Coverage
Cybersecurity professionals know all too well that visibility into potential threats is no longer a ...![]()
Beyond Traditional MDR: Why Modern Organizations Need Advanced Threat Detection
You Don’t Have to Settle for MDR That Sucks Frustrated with the conventional security measures pro...The Power of Human-Driven Cybersecurity: Why Automation Alone Isn’t Enough
Cyber threats are increasingly sophisticated, and bad actors are attacking organizations with greate...Importance of SOC Signal Assurance in MDR Solutions
In the dynamic and increasingly complex field of cybersecurity, ensuring the efficiency and effectiv...The Hidden Risks: Unmonitored Assets and Their Impact on MDR Effectiveness
In the realm of cybersecurity, the effectiveness of Managed Detection and Response (MDR) services hi...![]()
The Need for Symbiotic Cybersecurity Strategies | Part 2: Integrating Proactive Security Intelligence into MDR
In Part 1 of this series, The Need for Symbiotic Cybersecurity Strategies, we explored the critical ...Finding the Right Candidate for Digital Forensics and Incident Response: What to Ask and Why During an Interview
So, you’re looking to add a digital forensics and incident response (DFIR) expert to your team. Gr...![]()
The Need for Symbiotic Cybersecurity Strategies | Part I
Since the 1980s, Detect and Respond cybersecurity solutions have evolved in response to emerging cyb...![]()
Critical Start H1 2024 Cyber Threat Intelligence Report
Critical Start is thrilled to announce the release of the Critical Start H1 2024 Cyber Threat Intell...![]()
Now Available! Critical Start Vulnerability Prioritization – Your Answer to Preemptive Cyber Defense.
Organizations understand that effective vulnerability management is critical to reducing their cyber...![]()
Recruiter phishing leads to more_eggs infection
With additional investigative and analytical contributions by Kevin Olson, Principal Security Analys...![]()
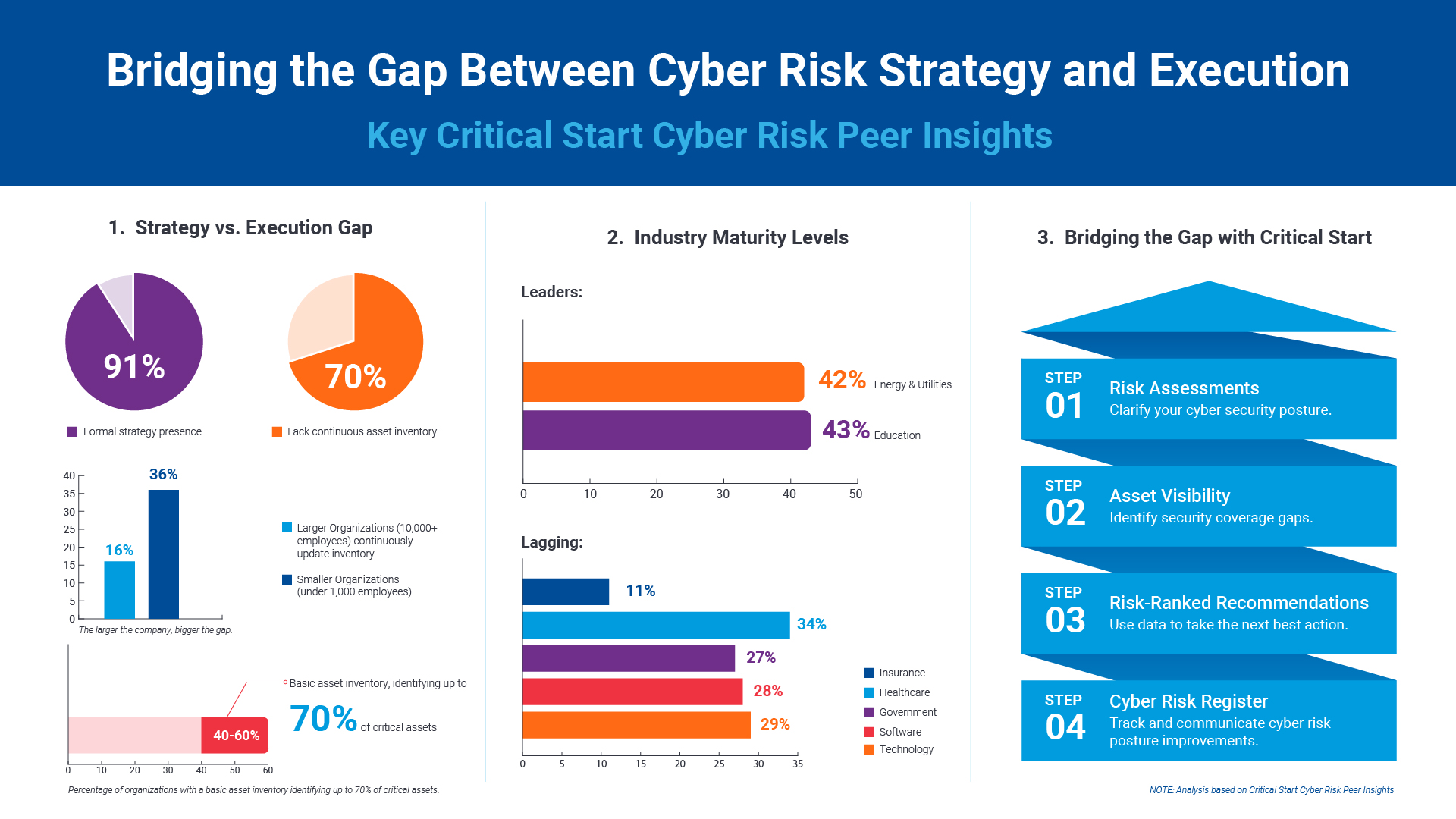
2024 Critical Start Cyber Risk Landscape Peer Report Now Available
We are excited to announce the release of the 2024 Critical Start Cyber Risk Landscape Peer Report, ...Critical Start Managed XDR Webinar — Increase Threat Protection, Reduce Risk, and Optimize Operational Costs
Did you miss our recent webinar, Stop Drowning in Logs: How Tailored Log Management and Premier Thre...Pulling the Unified Audit Log
During a Business Email Compromise (BEC) investigation, one of the most valuable logs is the Unified...![]()
Set Your Organization Up for Risk Reduction with the Critical Start Vulnerability Management Service
With cyber threats and vulnerabilities constantly evolving, it’s essential that organizations take...![]()
Announcing the Latest Cyber Threat Intelligence Report: Unveiling the New FakeBat Variant
Critical Start announces the release of its latest Cyber Threat Intelligence Report, focusing on a f...Cyber Risk Registers, Risk Dashboards, and Risk Lifecycle Management for Improved Risk Reduction
Just one of the daunting tasks Chief Information Security Officers (CISOs) face is identifying, trac...![]()
Beyond SIEM: Elevate Your Threat Protection with a Seamless User Experience
Unraveling Cybersecurity Challenges In our recent webinar, Beyond SIEM: Elevating Threat Prote...![]()
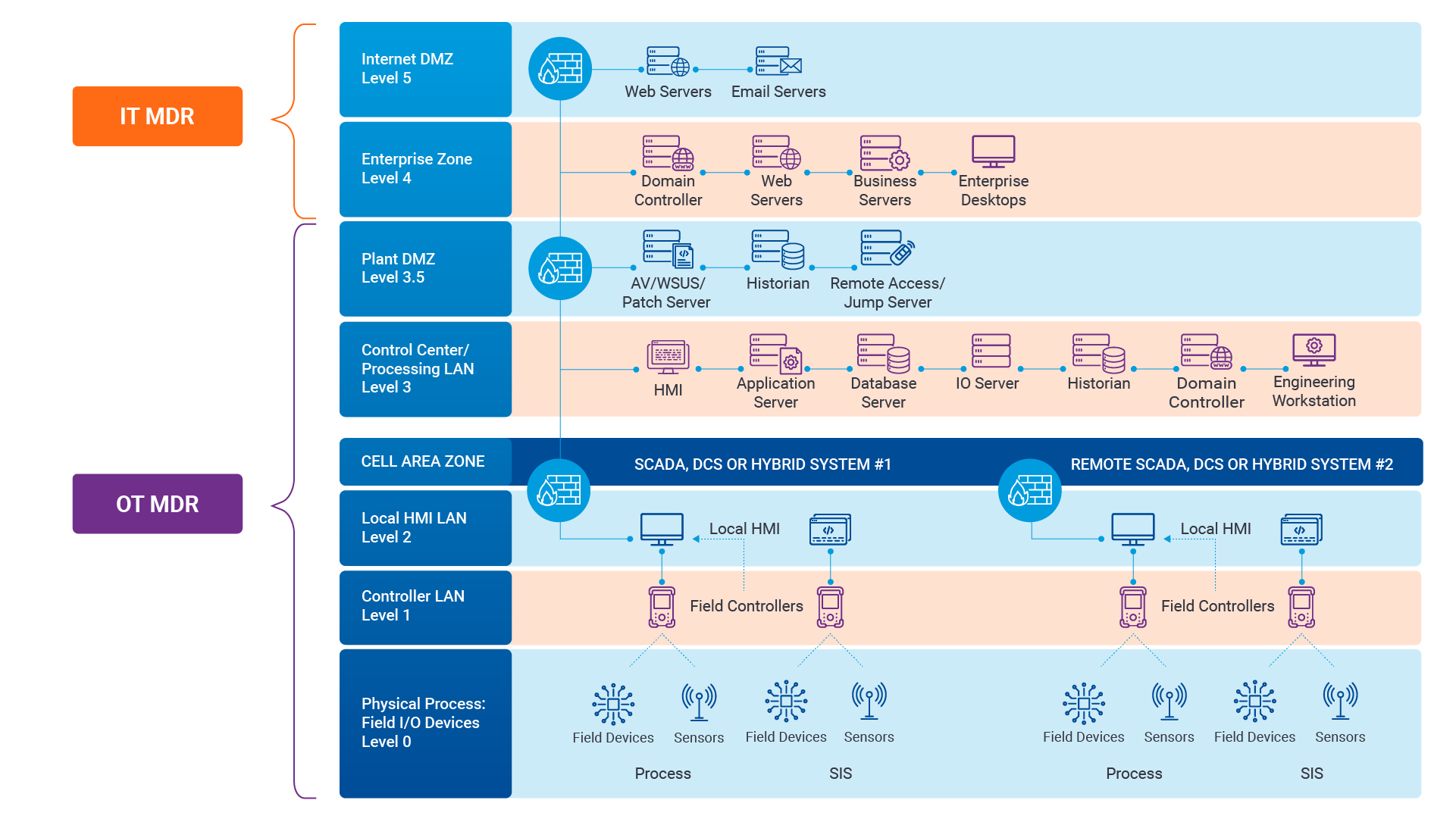
Navigating the Convergence of IT and OT Security to Monitor and Prevent Cyberattacks in Industrial Environments
The blog Mitigating Industry 4.0 Cyber Risks discussed how the continual digitization of the manufac...![]()
Critical Start Cyber Risk Peer Insights – Strategy vs. Execution
Effective cyber risk management is more crucial than ever for organizations across all industries. C...![]() Press Release
Press ReleaseCritical Start Named a Major Player in IDC MarketScape for Emerging Managed Detection and Response Services 2024
Critical Start is proud to be recognized as a Major Player in the IDC MarketScape: Worldwide Emergin...Introducing Free Quick Start Cyber Risk Assessments with Peer Benchmark Data
We asked industry leaders to name some of their biggest struggles around cyber risk, and they answer...Efficient Incident Response: Extracting and Analyzing Veeam .vbk Files for Forensic Analysis
Introduction Incident response requires a forensic analysis of available evidence from hosts and oth...![]()
Mitigating Industry 4.0 Cyber Risks
As the manufacturing industry progresses through the stages of the Fourth Industrial Revolution, fro...![]()
CISO Perspective with George Jones: Building a Resilient Vulnerability Management Program
In the evolving landscape of cybersecurity, the significance of vulnerability management cannot be o...![]()
Navigating the Cyber World: Understanding Risks, Vulnerabilities, and Threats
Cyber risks, cyber threats, and cyber vulnerabilities are closely related concepts, but each plays a...The Next Evolution in Cybersecurity — Combining Proactive and Reactive Controls for Superior Risk Management
Evolve Your Cybersecurity Program to a balanced approach that prioritizes both Reactive and Proactiv...![]()
CISO Perspective with George Jones: The Top 10 Metrics for Evaluating Asset Visibility Programs
Organizations face a multitude of threats ranging from sophisticated cyberattacks to regulatory comp...- Webinar
Are Critical Threats Slipping Through Your Defenses?
Modern security teams are buried in noisy alerts and stretched thin. Even with powerful tools like M... ![]()
Ransomware in Gaming: How Casinos Can Defend Against Modern Cyber Threats
Hackers aren’t gambling. They know exactly where to hit. And for gaming companies, the stakes ...- eBook
Ditch the Black Box: Get Transparent MDR with Critical Start
Tired of MDR providers leaving you in the dark? We totally get it. Our eBook, Unmatched Transparency...
Newsletter Signup
Stay up-to-date on the latest resources and news from CRITICALSTART.
Thanks for signing up!