Threat Protection Beyond the Endpoint with MDR Solutions and Services
- Services
- Solutions
- Why Critical Start?
- Resources
- About
- Partner Programs
- Breach Response
- Contact an Expert
- Intelligence Hub
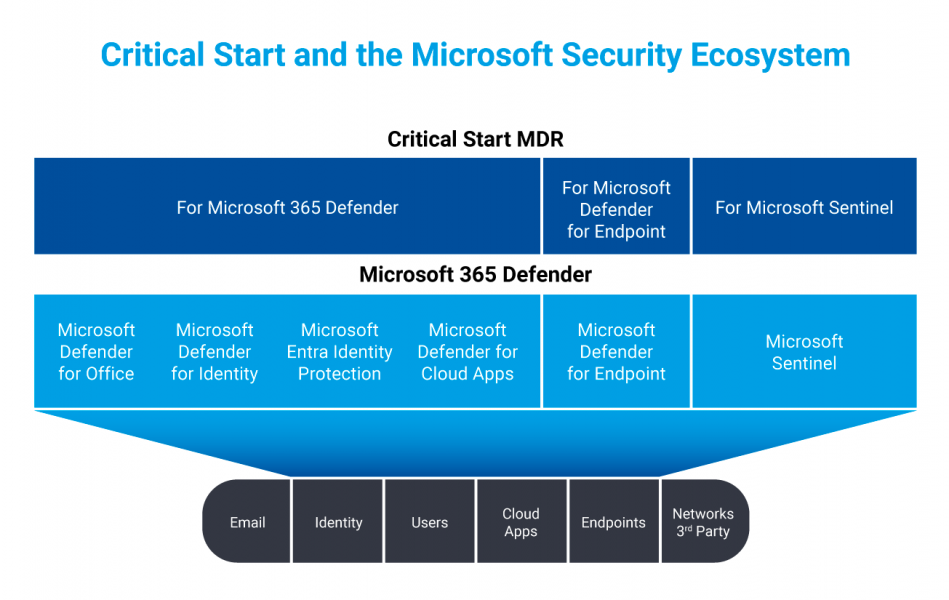
Strengthen your SIEM + XDR defenses to protect against today’s and tomorrow’s threats with Critical Start and Microsoft
Bringing together Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) tools and intelligence enhances threat protection across your digital estate. When you combine Microsoft Sentinel with the Microsoft Defender Security suite it improves your ability to see attacks across the organization, secure end users and secure your multi-cloud infrastructure.
But you still need the people – the Microsoft expertise and proven methodologies – to derive true value for security outcomes. Don’t let the skills gap impede your ability to operate with maximum protection.
Access the Right Expertise and Strategy for Integrated Threat Protection

Consolidated visibility, across SIEM and XDR, of your Microsoft environment – all in one portal.
Protection for advanced use cases including identity, email and cloud, with an all-in-one security approach that’s applied at every security layer.
Reduce risk exposure with human-led monitoring, rapid investigation, continuous threat hunting and response.
Strengthen security maturity with an ongoing, strong partnership that helps you get the most out of your Microsoft Security investment.
-

Security Director
We have a pretty wide digital footprint with 6,000 employees and 42,000 students across 40 schools. With the expanding attack surface and increase in ransomware attacks, our small security team needed the expertise to maximize our Microsoft A5 Security. Critical Start has dramatically improved our security posture by helping us truly operationalize Microsoft Sentinel and Microsoft 365 Defender and by providing us 24x7x365 coverage to be able to investigate and respond to increasingly complex attacks across users, devices and our cloud apps.”
Microsoft Sentinel, Microsoft Defender for Endpoint, and Microsoft 365 Defender user
How Critical Start Helps You Realize Value from Microsoft 365 Defender
-
 Protect everything, everywhere.
Protect everything, everywhere.Given the volume and complexities of identities, data, applications, devices, and infrastructure, it’s essential to learn how secure your organization is now and how to mitigate and protect against threats moving forward.
- Develop a strategic plan customized for your organization’s priorities
- Implementation and onboarding focused on applying Microsoft security best practices and high-fidelity threat detection
- Continuous fine-tuning as new risks are identified
-
 Extend your capabilities to quickly detect and respond to threats
Extend your capabilities to quickly detect and respond to threatsWhen minutes count, our Microsoft security experts can become and extension of your team and provide remediation and response actions to the threat as soon as it’s detected.
You’ll get:
- 24x7x365 monitoring, investigation and resolution of all alerts and incidents
- Management of out-of-the-box Indicators of Compromise (IOCs)
- Freedom from intelligence overload
- Visibility across your Microsoft security controls in one portal
-
 Advance security maturity with a focus on continuous improvement
Advance security maturity with a focus on continuous improvementWith Critical Start, you have access to end-to-end solutions and services that move with you on your Defender journey, helping anticipate risk and strengthening security posture.
- Microsoft Security tools and ZTAP configured to eliminate false positives (>99% of alerts)
- Solutions for use cases like email phishing, brute force and stolen credential attacks, and attacks against cloud apps
- Indicators of Compromise (IOCs) mapped to MITRE ATT&CK® Framework
- Coverage of every alert and incident with 1-hour Time to Detection (TTD) and Median Time to Resolution (MTTR) SLAs

Featured resources to learn how to optimize SIEM + XDR
-
 Blog
BlogXDR 101: What is Extended Detection and Response
Extended Detection and Response (XDR) is by far one of the hottest topics and trends in cybersecurity today. Learn what XDR is, why its important, and how it works with MDR services.
-
 eBook
eBookRansomware Protection Guide
This guide outlines best practices on how to protect and defend against ransomware attacks leveraging the Microsoft Security stack.
-
 Blog
BlogBeyond the Endpoint: Detect and Disrupt User Account Attacks
Learn about capabilities developed by Critical Start to extend Managed Detection and Response services to support Microsoft 365 Defender’s user account attacks and credential misuse detection alerts.
-
 Blog
BlogThree Reasons Companies Fall Victim to Ransomware – and One Big Way the Game is Changing
What are the key reasons companies fall victim to ransomware? In this blog, we explore 3 main reasons and one thing about ransomware that might surprise you.