- Services
- Solutions
- Why Critical Start?
- Resources
- About
- Partner Programs
- Breach Response
- Contact an Expert
- Intelligence Hub
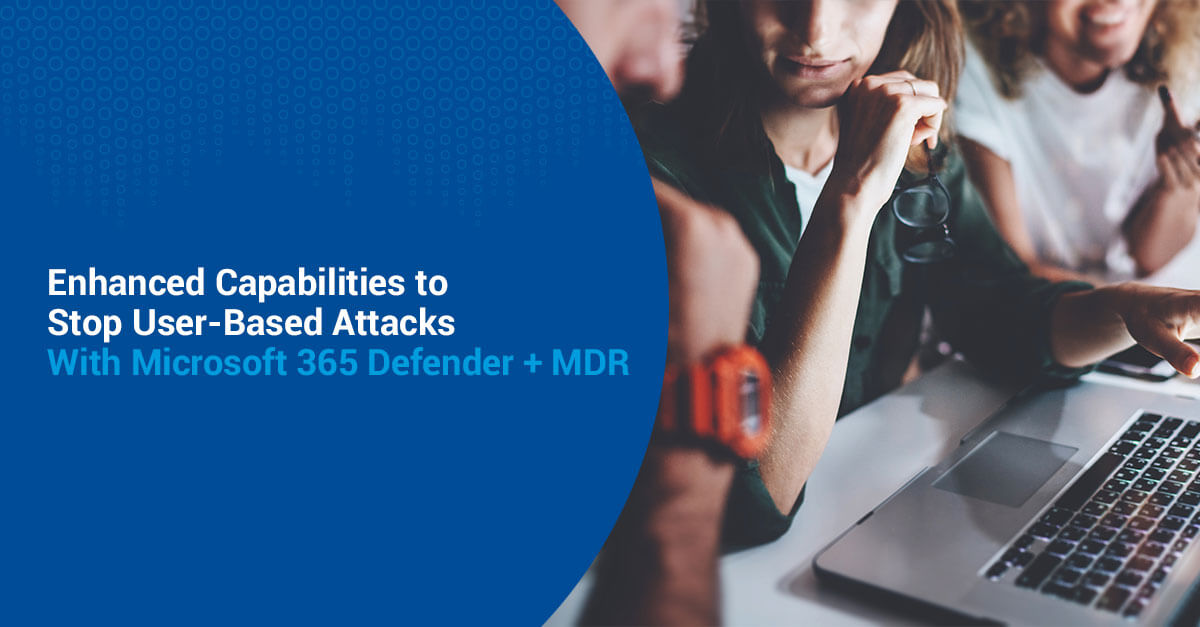
Protect Against User Account Attacks with SOC Solutions and Services
Disrupt user account attacks across your domain – endpoint, email user credentials and cloud apps
As cyber defender teams add additional security technologies beyond the endpoint to detect attacks against user accounts, the additional volume of alerts (many still being false positives!) creates an exponential burden on these teams to investigate each and every alert. Even missing one successful credential attack can lead to data compromise.
Further compounding this problem, adversaries have multiple attack vectors to steal, harvest, and misuse user account credentials which severely limit how endpoint-oriented response actions can fully disrupt an active misuse of a stolen user credential across authentication sources and cloud applications.
Speed up user account investigation and response 24x7x365 across the attack surface

Prevent identities from being compromised by identifying potential risks related to user accounts and credential misuse.

All-in-security integration with access and visibility across Microsoft Security in one portal.
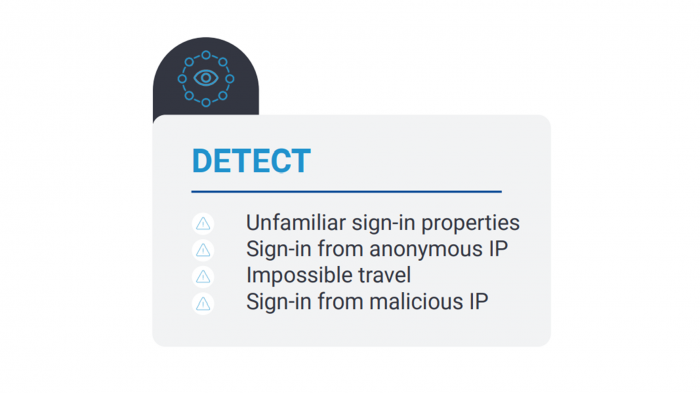
Detect and disrupt threat actors attempting to infiltrate user accounts at any point during the attack chain.
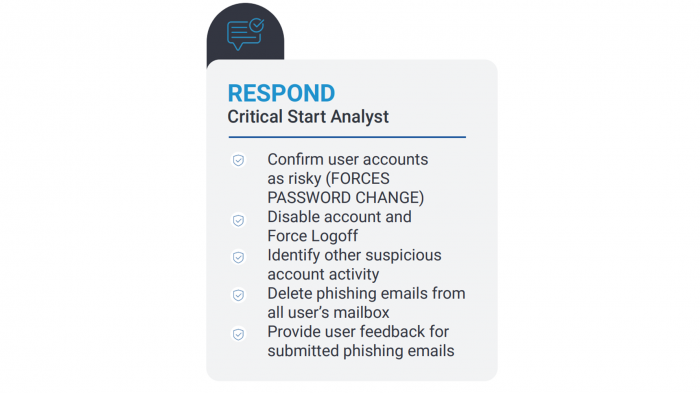
Post-breach remediation of compromised user accounts means our experts will take response actions on your behalf and work with your team until the case is resolved.
How Critical Start Protects Against User Account Attacks
-
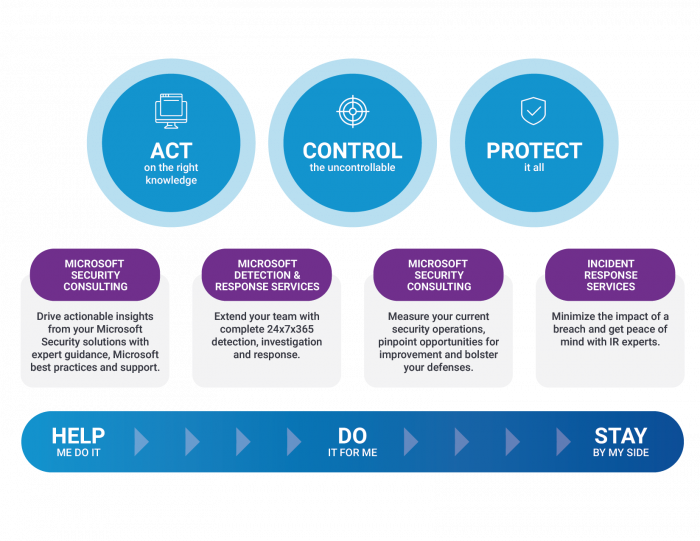 Protect your data, infrastructure and people
Protect your data, infrastructure and peopleGetting identity and threat protection right is a critical part of Microsoft 365 Defender.
We will help you find identity risk happening in your environment, gain insights into your application landscape and improve your identity security posture.
We provide 24x7x365 cross-domain threat protection. Our seamless integration with Microsoft Security brings unmatched visibility to detect every threat while investigating and resolving every incident across endpoints, user accounts and cloud apps.
-
 Improve operational efficiency and team effectiveness
Improve operational efficiency and team effectivenessWe bring the detection, investigation and response capabilities, Microsoft Security knowledge & best practices, Indicator of Compromise (IOCs) management and Level 1 and Level 2 tools support that free up your team to focus on strategic initiatives.
Our Managed Detection and Response services support Microsoft 365 Defender’s user account attacks and credential misuse detection alerts. These capabilities go beyond the endpoint to detect user attacks against authentication sources, applications, and attempts at credential harvesting.
-
 Stay ahead of advanced threats
Stay ahead of advanced threatsMinutes count. Critical Start has natively integrated our web interface and MOBILESOC® mobile application with Microsoft 365 Defender APIs to create a single interface to perform manual and automated response actions.
Featured resources to learn how to protect against user-based attacks
-
 Whitepaper
WhitepaperSimplify your Microsoft Security Operations for Identity-Based Alerts
Examine an optimal approach to detect and address identity-based alerts in a Microsoft environment, and its benefits.