- Services
- Solutions
- Why Critical Start?
- Resources
- About
- Partner Programs
- Breach Response
- Contact an Expert
- Intelligence Hub
CRITICALSTART® MDR Services for CrowdStrike® Falcon®
Achieve the full operating potential of your CrowdStrike Pro, Enterprise, or Elite investments
The combination of CrowdStrike Falcon with CRITICALSTART® Managed Detection and Response (MDR) services goes far beyond just monitoring alerts. It increases visibility across hybrid device types and operating systems to stop the most advanced attacks, reduce risk exposure, eliminate alert fatigue, and optimize the efficiency of security operations centers (SOC).
Key Benefits
A simplified view of everything
Consolidated and improved visibility of your environment all in a single interface.
Reduce the noise
Get fewer false positives over time which dramatically reduces alert fatigue and analyst burnout.

Improve security posture
Our Cyber Research Unit (CRU) helps you stay ahead of the latest threats by building, enriching and adding threat intelligence to your security tools.
Increase your SOC’s efficiency and productivity
We do all the heavy lifting for you, so you don’t have to.
How Our MDR Service for CrowdStrike Falcon Works
Critical Start MDR adapts to your environment to deliver the full power of CrowdStrike Falcon Pro, Enterprise, or Elite.
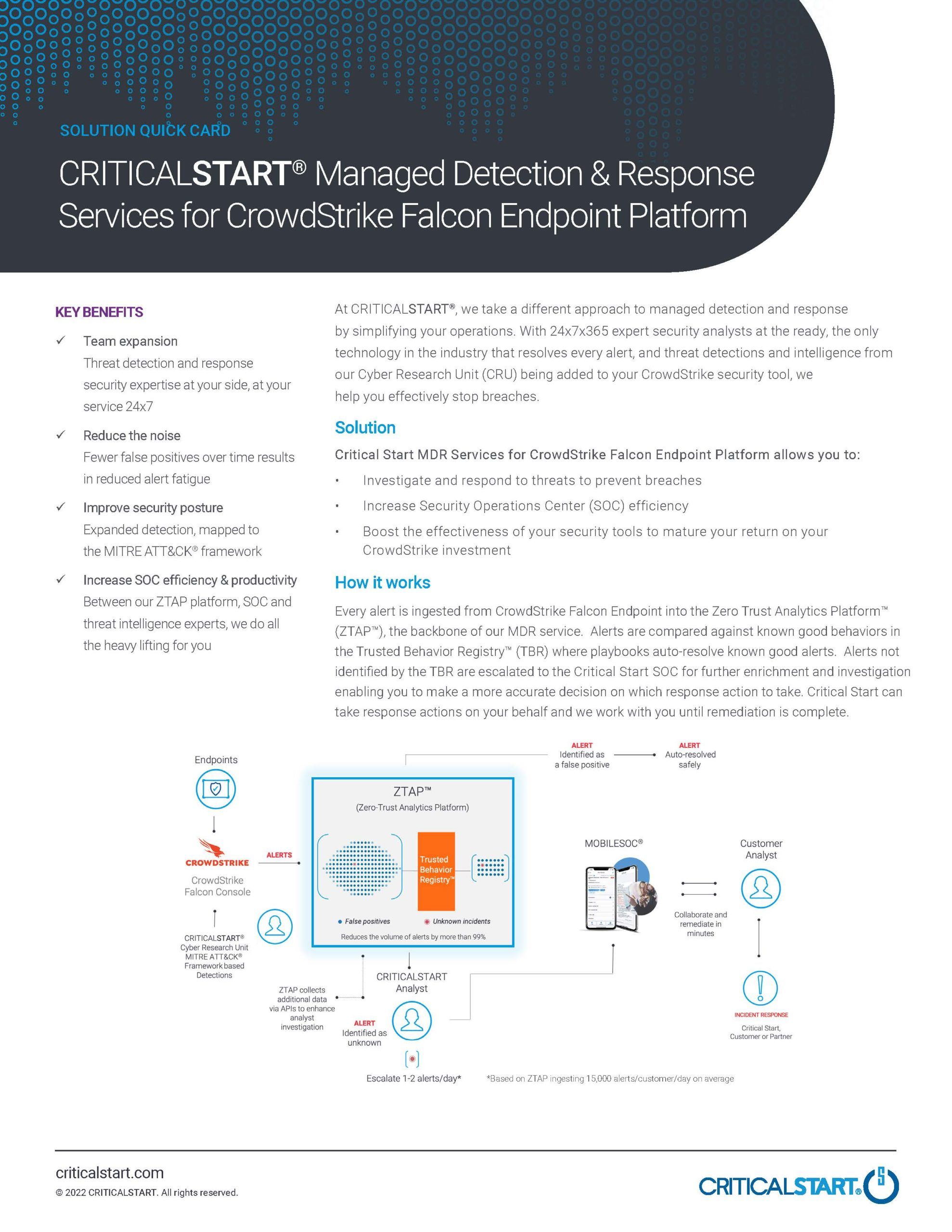
Our bi-directional integration ingests every endpoint alert from CrowdStrike Falcon into our Cyber Operations Risk and Response™ platform, where they’re compared against known good behaviors in the Trusted Behavior Registry® (TBR) and playbooks auto-resolve known good alerts at scale. Alerts not matching the TBR are escalated to our Risck and Security Operations Center (RSOC) analysts for further enrichment and investigation. Best of all, we can take response actions on your behalf, and we will work with you until remediation is complete.
Hear from Our Customers
-

Justin Hadley
The managed detection and response service has significantly increased our analysts’ efficiency to the point that they can focus on other areas of the business.
Sr Manager, Security Engineering, Alkami
How We Work with You
We’re with you every step of the way – from onboarding through maturity.

Onboard quickly:
We will get you up and running as fast as possible: 4-6 weeks on average with total time to first value of approximately 5-10 business days.
Personalize based on your unique requirements:
We continue to add value to your implementation by tailoring our MDR services to your unique needs through playbooks and procedures adapted to your environment to reduce false positives.


Investigate and resolve alerts:
Once you’re up and running, our platform and our security analysts will monitor your environment 24x7x365 for potential threats. You can expect to see an approximate reduction in false positives of 90% on the first day of production monitoring.
Mature your CrowdStrike investment:
We want to help you get the most out of your CrowdStrike Falcon tools, so we’re with you every step of the way. Your Customer Success Manager will check in with you regularly to make sure we’re meeting your expectations and our MDR services are helping you achieve your security goals.

Why Critical Start MDR?
Resolve, not suppress
We resolve every alert and only forward those that truly warrant additional investigation by your security team.
- Resolve more than 99% of alerts
- Escalate less than 0.01% of alerts
Ready to respond 24/7/365
Our security analysts help you contain and extinguish threats as quickly as possible to stop them from spreading. They:
- Operate as an extension of your security team
- Triage and investigate alerts that are not auto-resolved by our platform and the TBR
- Use your tools and our platform to respond to alerts on your behalf — depending on mutually agreed-upon rules of engagement
- Function as an open book with 100% transparency and visibility into every action taken
Experts in threat detection
The Threat Detection Engineering (TDE) team develops and enriches new detections and IOCs. They also map detection to the industry-leading MITRE ATT&CK® Framework, ensuring you are protected against the latest attacker Techniques, Tactics, and Procedures (TTPs).
Fast resolution with MOBILESOC®
MobileSOC puts the power of our platform in your hands, giving you the ability to triage, escalate, and isolate attacks in-the-moment from your iOS or Android phone regardless of your location or time of day.
-
 Quick Card
Quick CardMDR Services for CrowdStrike Falcon
Critical Start integrates with CrowdStrike Falcon to offer a full Managed Detection and Response (MDR) service using Critical Start’s proprietary MDR platform. By ingesting CrowdStrike endpoint detection events into the platform, we effectively detect and resolve every alert generated.
MDR for multiple EDR, SIEM, and XDR tools
We offer MDR services for multiple tools, all supported by a single platform and accessible on the go through our MobileSOC app, making these easy for our customers that work with multiple security tool vendors.