- Services
- Solutions
- Why Critical Start?
- Resources
- About
- Partner Programs
- Breach Response
- Contact an Expert
- Intelligence Hub
What You’ll Learn
Within this guide, you’ll find step by step guidance to help you mature your Microsoft Security tools and approach breach prevention with simplified threat detection and response.
-
-
Pulling the Unified Audit Log
During a Business Email Compromise (BEC) investigation, one of the most valuable logs is the Unified...![]()
Announcing the Latest Cyber Threat Intelligence Report: Unveiling the New FakeBat Variant
Critical Start announces the release of its latest Cyber Threat Intelligence Report, focusing on a f...Cyber Risk Registers, Risk Dashboards, and Risk Lifecycle Management for Improved Risk Reduction
Just one of the daunting tasks Chief Information Security Officers (CISOs) face is identifying, trac...![]()
Beyond SIEM: Elevate Your Threat Protection with a Seamless User Experience
Unraveling Cybersecurity Challenges In our recent webinar, Beyond SIEM: Elevating Threat Prote...![]()
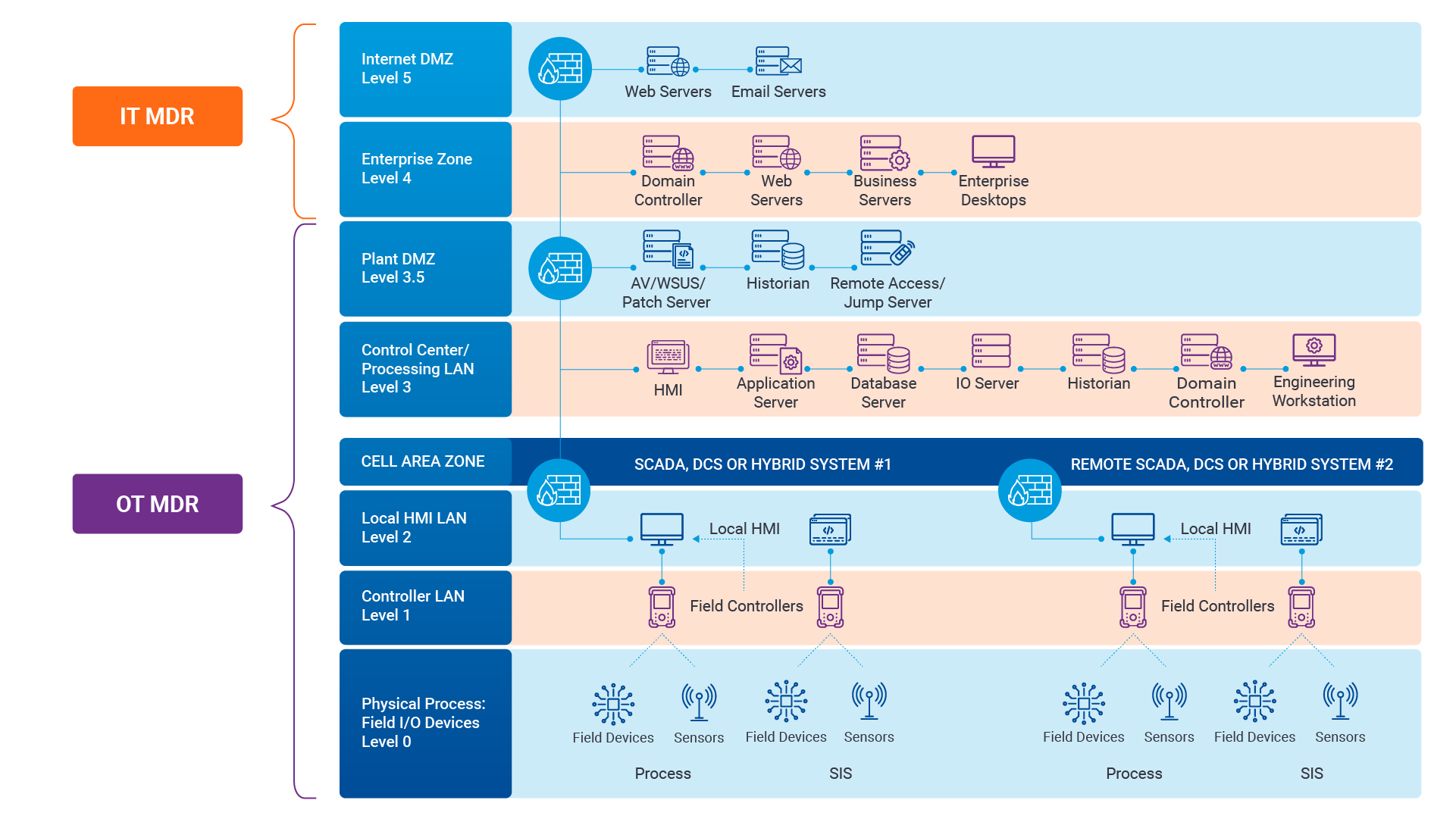
Navigating the Convergence of IT and OT Security to Monitor and Prevent Cyberattacks in Industrial Environments
The blog Mitigating Industry 4.0 Cyber Risks discussed how the continual digitization of the manufac...![]()
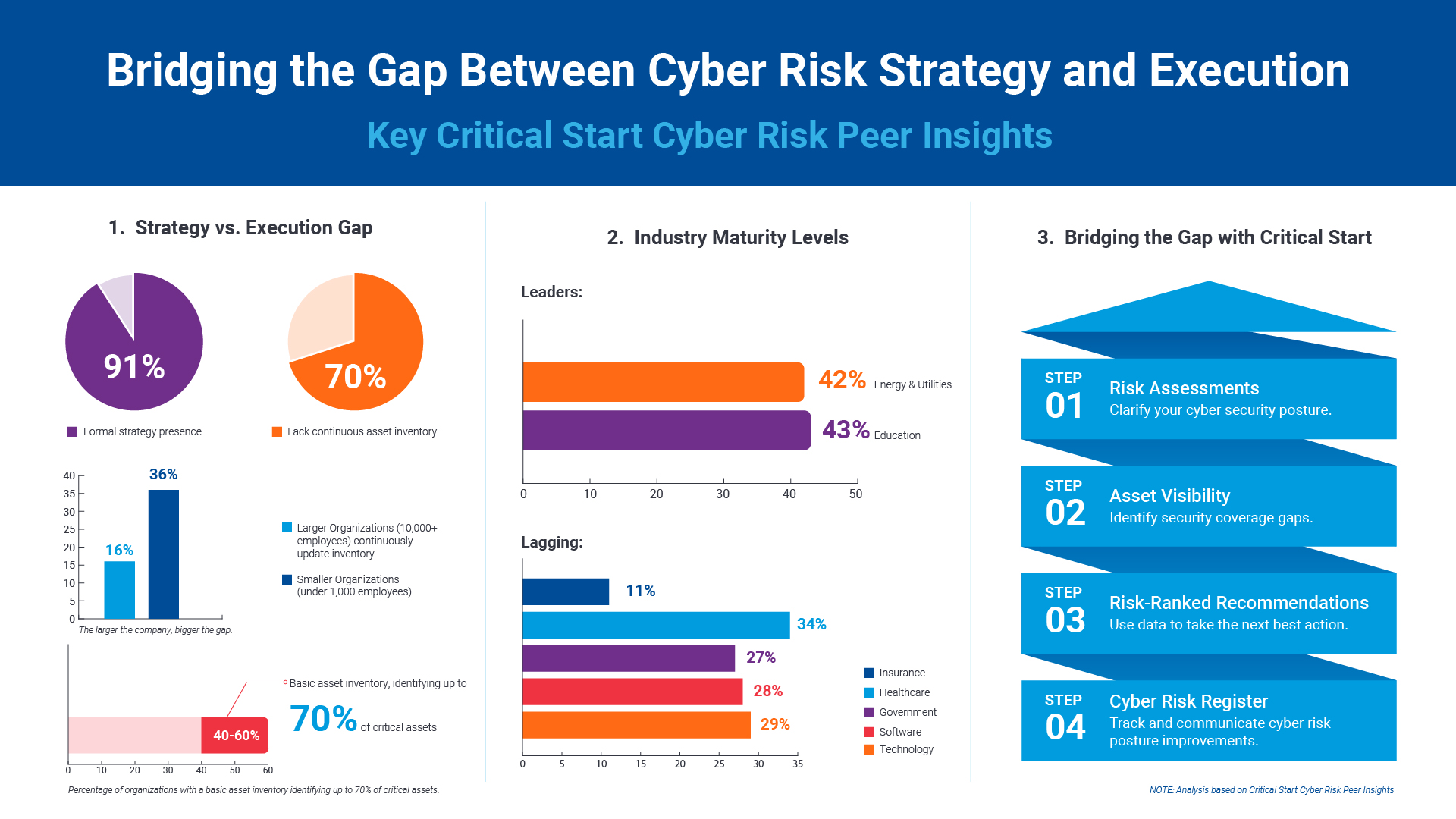
Critical Start Cyber Risk Peer Insights – Strategy vs. Execution
Effective cyber risk management is more crucial than ever for organizations across all industries. C...![]() Press Release
Press ReleaseCritical Start Named a Major Player in IDC MarketScape for Emerging Managed Detection and Response Services 2024
Critical Start is proud to be recognized as a Major Player in the IDC MarketScape: Worldwide Emergin...Introducing Free Quick Start Cyber Risk Assessments with Peer Benchmark Data
We asked industry leaders to name some of their biggest struggles around cyber risk, and they answer...Efficient Incident Response: Extracting and Analyzing Veeam .vbk Files for Forensic Analysis
Introduction Incident response requires a forensic analysis of available evidence from hosts and oth...![]()
Mitigating Industry 4.0 Cyber Risks
As the manufacturing industry progresses through the stages of the Fourth Industrial Revolution, fro...![]()
CISO Perspective with George Jones: Building a Resilient Vulnerability Management Program
In the evolving landscape of cybersecurity, the significance of vulnerability management cannot be o...![]()
Navigating the Cyber World: Understanding Risks, Vulnerabilities, and Threats
Cyber risks, cyber threats, and cyber vulnerabilities are closely related concepts, but each plays a...The Next Evolution in Cybersecurity — Combining Proactive and Reactive Controls for Superior Risk Management
Evolve Your Cybersecurity Program to a balanced approach that prioritizes both Reactive and Proactiv...![]()
CISO Perspective with George Jones: The Top 10 Metrics for Evaluating Asset Visibility Programs
Organizations face a multitude of threats ranging from sophisticated cyberattacks to regulatory comp...![]() Solutions Brief
Solutions BriefMaximize the Value of Microsoft Security
Maximize the value of Microsoft Security with MDR Services and Microsoft Security Consulting. Read t...![]() Datasheet
DatasheetCritical Start Cybersecurity Consulting for Microsoft Security
The complexity of today’s security landscape – combined with an increase in incidents, overall w...![]() eBook
eBookCritical Start Guide to MDR and Microsoft Security
Microsoft Security tools such as Microsoft 365 Defender, Microsoft Defender for Endpoint and Microso...
Newsletter Signup
Stay up-to-date on the latest resources and news from CRITICALSTART.
Thanks for signing up!